Blog
Learn about software supply chain security and Endor Labs
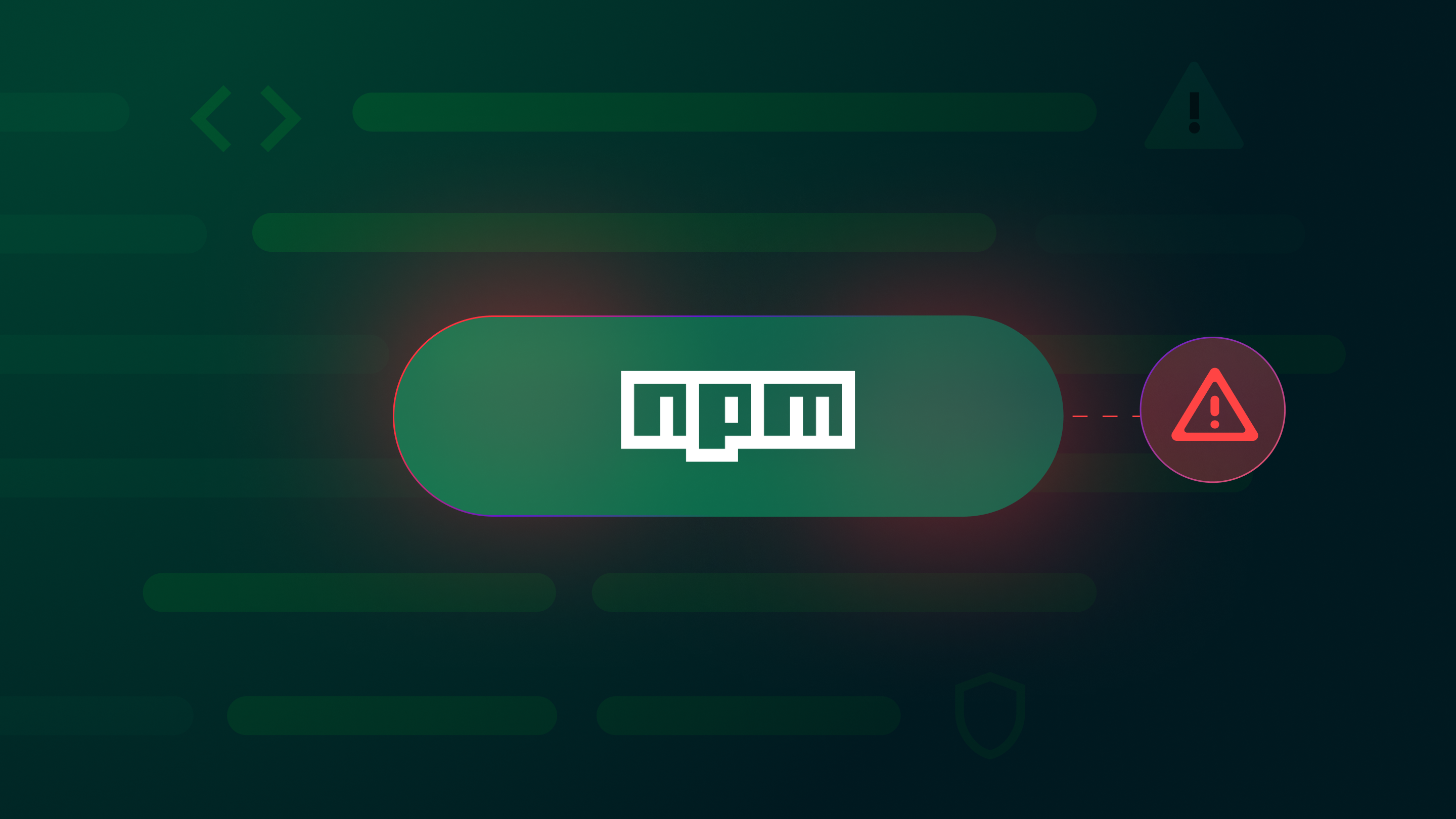
CVE-2025-54313: eslint-config-prettier Compromise — High Severity but Windows-Only
CVE-2025-54313 tracks a supply chain attack on eslint-config-prettier, where four malicious versions of a popular npm library targeted Windows machines with a remote-code execution payload. Learn how it happened and how to stay safe.
Book a Demo
Protect your open source dependencies, secrets, and CI/CD pipelines without slowing down devs.