Detect and block software supply chain attacks































































How Endor Labs blocks malicious packages

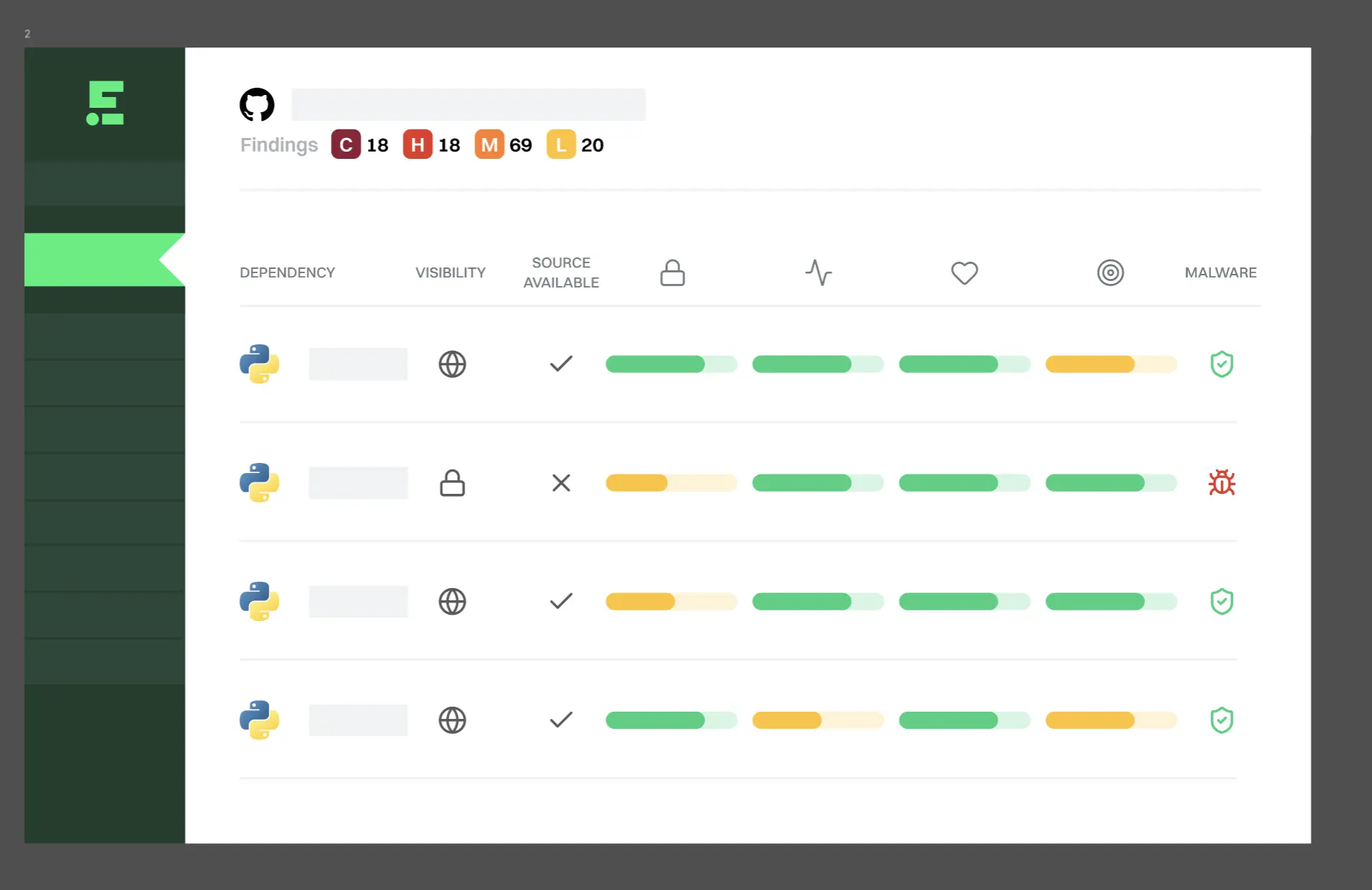
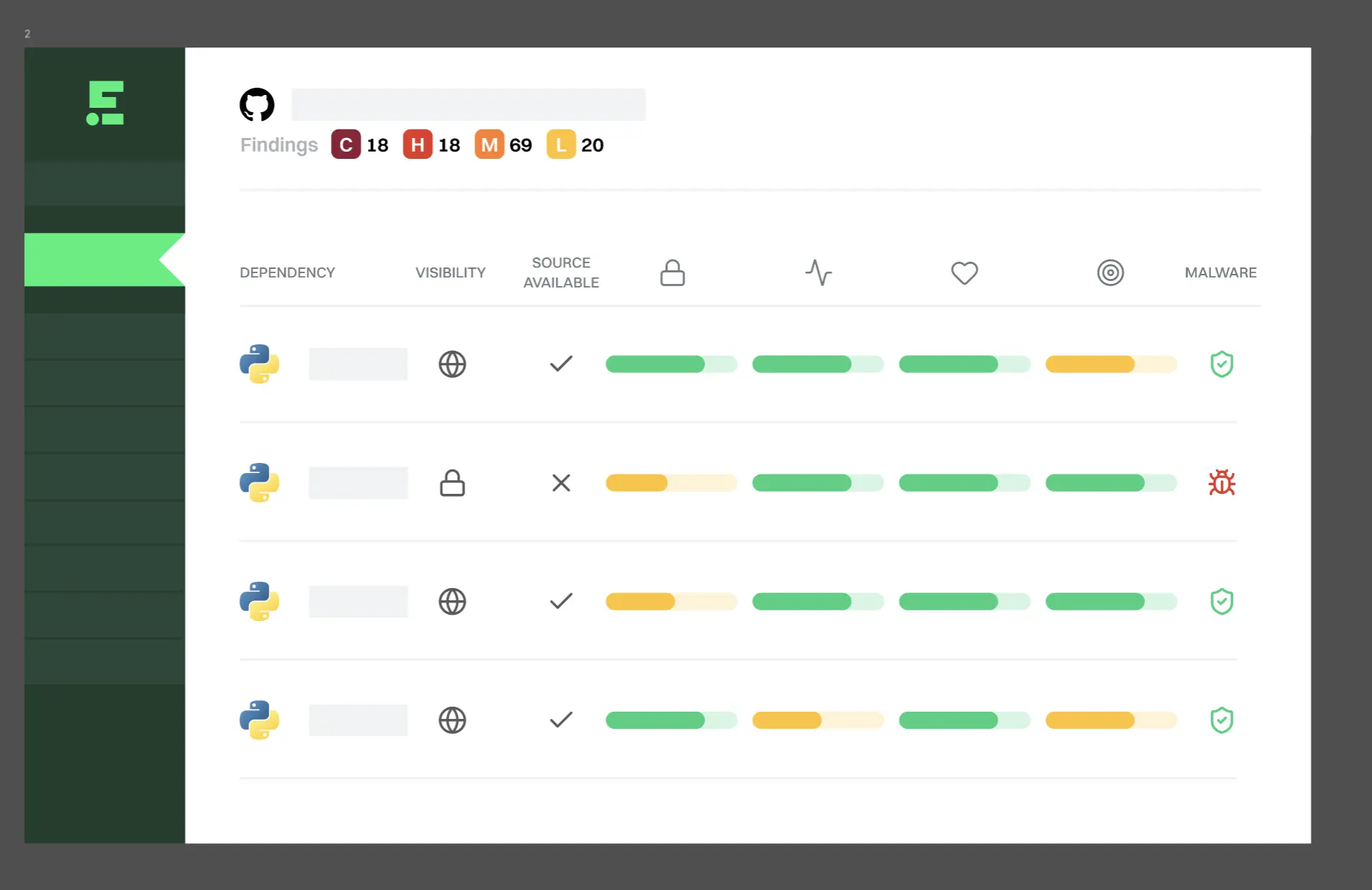
Detect malicious dependencies
Endor Labs scans every new package uploaded to npm, PyPI, and other registries for malicious code, typosquats, and more.
Block threats with Package Firewall
Block policy-violating packages in real time using proprietary intelligence and rapid analysis pipelines.

Enforce proactive policies
Define proactive policies to automatically block or allow packages based on your risk tolerance.
Endor Labs catches malicious dependencies before we even hear about a CVE. Their security research team goes beyond automated detection to help us verify the threat so we can act early and decisively.”


Related Resources
Every newly published package across npm, PyPI, and other registries is analyzed using agentic reasoning, static analysis, behavioral inspection, and 150+ other signals — catching malicious code, hidden payloads, and suspicious maintainer activity that traditional scanners miss.
Compromised maintainer accounts, typosquats, dependency confusion, install-time scripts, obfuscated payloads, credential stealers, and other malicious behaviors across open-source ecosystems.
Traditional SCA flags known vulnerabilities after CVEs are published. Endor Labs detects malicious packages in real time at upload, then blocks them before they reach developer machines or CI pipelines.
Yes. Define policies based on cooldown periods, unpinned dependencies, unused dependencies, license type, maintainer reputation, and other risk signals — not just malware classification. Enforce your own risk standards beyond what's publicly known to be malicious.
The same policy engine governs both human developers and AI coding agents, so packages installed by Claude Code, Cursor, or other AI tools face identical guardrails before reaching sandbox or cloud environments.
No. Package Firewall runs in the background between your artifact repository and the public registry — safe packages flow through transparently, and developers don't change how they work.
When connected directly to the firewall, they see an HTTP 403 Forbidden error with a clear message. When going through some registries (like Artifactory), that 403 may appear as a 404 Not Found in the CLI.
Yes. Endor Labs’ Package Firewall integrates with JFrog Artifactory today, with support for Nexus and AWS CodeArtifact coming soon. Private packages are fetched from your artifact repository; public packages are checked through the proxy.



