Featured resources

Malware
Security
Security
Malware
News
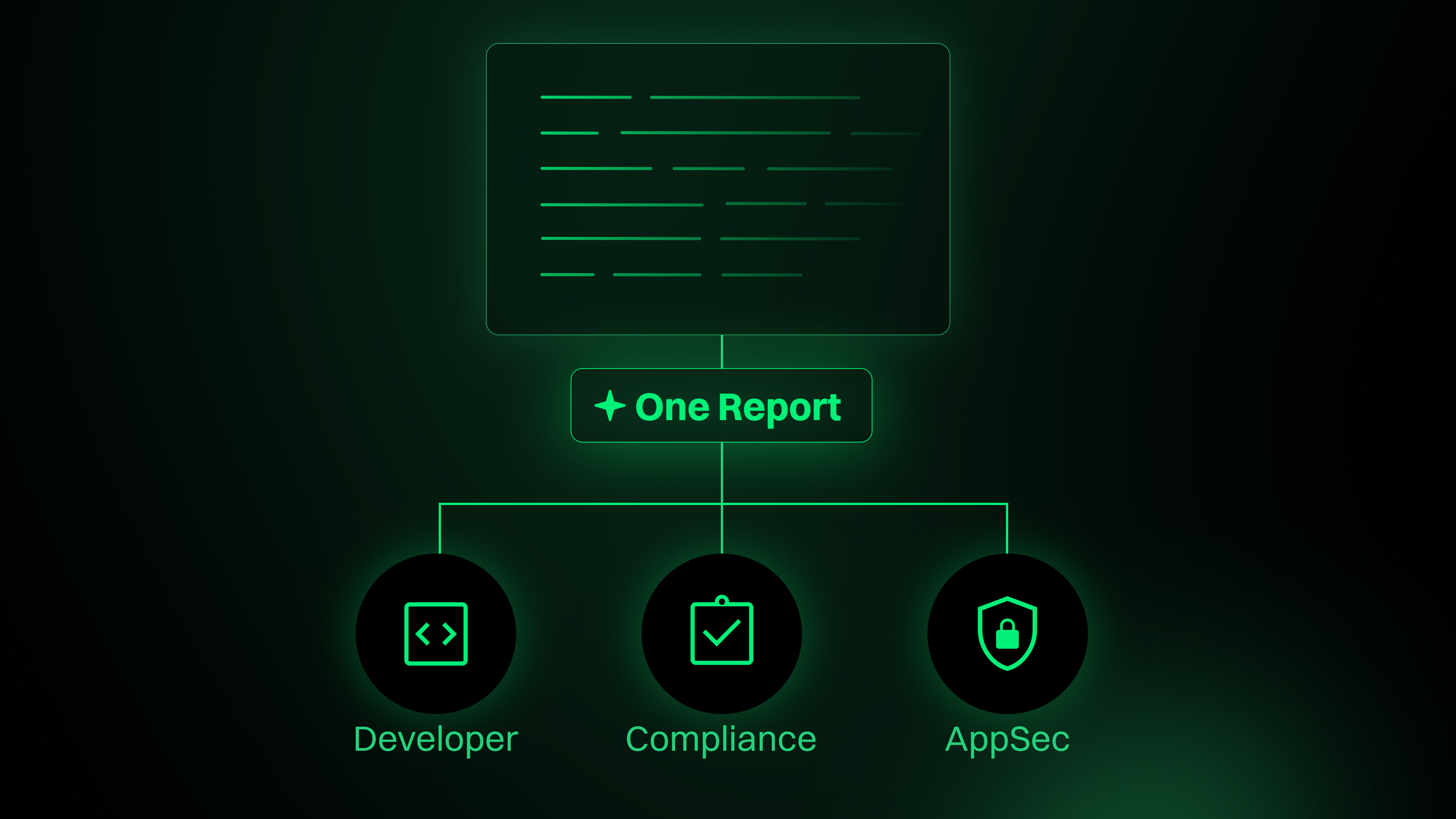
Open Source
Malware
News
Security
Open Source
Partner blogs
Malware
News
Open Source
Security
AI/ML
Malware
Security
AI/ML
Open Source
Security
Malware
Open Source
Security
AI/ML
Want to stay in the loop?
Sign up for our newsletter.