Today, we're launching AURI by Endor Labs, the security intelligence layer for AI coding agents. And we're making AURI available to everyone: our Skills plugin, MCP, and CLI are now free for developers. You can use them to detect vulnerabilities and exposed secrets in your code and open source dependencies, block malware attacks, and fix security bugs.
AI is transforming the software development lifecycle. AI agents are writing, reviewing, and shipping code across editors, CI pipelines, and in cloud environments. This is a massive win for developers, but security hasn’t kept pace.
Vulnerability backlogs keep growing, traditional tools generate more noise than signal, and bolting security on after the fact doesn't work when the pace of development has fundamentally changed. Meanwhile, attackers are adopting AI, too. New AI-generated exploits and sophisticated software supply chain attacks are emerging faster than defenders can respond.
But AI is also changing that calculus. We believe there is a once-in-a-generation opportunity to shift security down into the architecture of agentic coding itself, rather than as a series of gates and checks that slow down software development.
We've already shown what this looks like: AURI has detected novel, zero-day vulnerabilities as the engine behind Endor Labs' AI SAST, and AURI’s security agents are catching emerging malware campaigns across npm, PyPI, Maven, and other package ecosystems in real time.
We built AURI to put security intelligence directly into the hands of developers, defenders, and their agents so they can stay ahead of attackers.
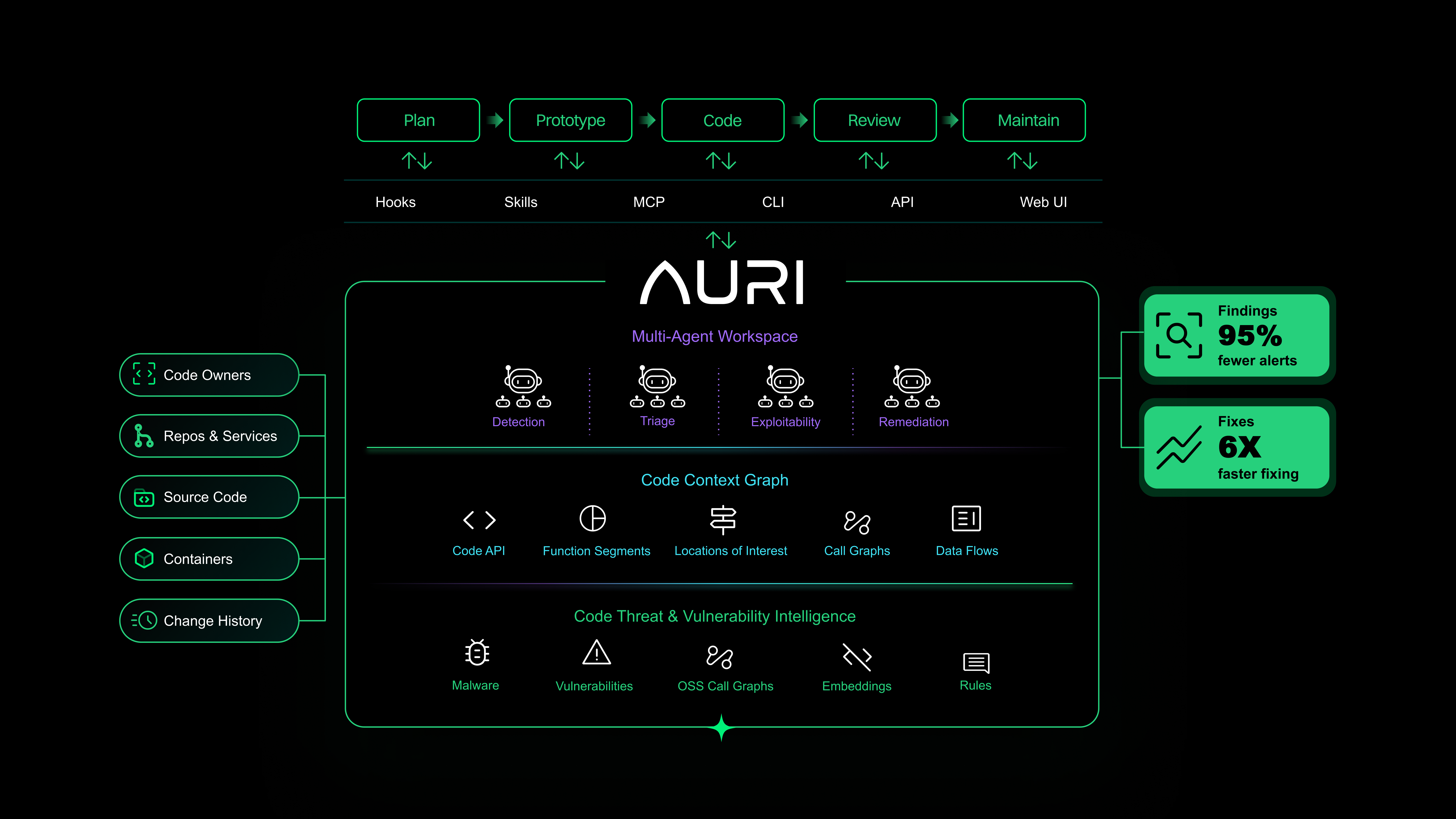
AURI works everywhere you do
Security has to work wherever software development happens. Traditionally, that happened in the integrated development environment (IDE) or in pull requests (PRs). But today, agents run in the code editor, during code review, in the CI pipeline, and even fully in the cloud on their own infrastructure.
That's why we're launching AURI alongside a partnership with OpenHands. OpenHands represents the future of agentic software development. You can work locally, run in the CI pipeline, or simply delegate tasks via Slack to agents working in the cloud. AURI integrates with these agents via a plugin that bundles dozens of useful security skills into a full-stack security review spanning code, secrets, dependencies, and container images.
The demo below shows the OpenHands CLI using AURI to scan and fix several vulnerabilities across first-party code and third-party dependencies. You can scale this same workflow to run in CI, or independently in the cloud.
The missing context for agentic software development
Every AI coding agent has the same blind spot: it can write code, but it can't see your full application context, or how your code, dependencies, container images, and services interact. The latest LLMs, like Claude Sonnet 4, can write functionally correct code 61% of the time. But only 10% of code written by AI agents is both functionally correct and secure.
Think about how a senior engineer actually reviews code. They don't just use grep to search for CVEs. They carry a mental model of the entire system, and trace how data flows from a user input through multiple services. They check whether a vulnerable function is actually reachable. They know that the auth middleware two layers up already mitigates the finding that a scanner just flagged as critical.
All of this context allows them to separate risk from the noise, and this context is exactly what AI agents are missing. So we built it.
Security intelligence for AI coding agents
At the core, AURI is powered by the code context graph, a complete model of who wrote the code, where the service sits in your infrastructure, the change history, and the code, dependencies, and container images that form the application. It’s a graph of the software artifact and the surrounding organizational context rather than a static inventory of components.
AURI can then orchestrate its own agents (with their own sub-agents) that navigate the code context graph to detect, triage, validate, and remediate vulnerabilities. These agents can also use AURI’s security intelligence, which includes the industry’s largest labeled database of code vulnerabilities. This includes the exact code diffs and functions that introduced each vulnerability, the category of flaw that caused the vulnerability (e.g. SQL injection), and how the vulnerability was patched by the maintainers.
Together, this gives AURI’s agents unparalleled insights into both how your code works and how attackers could exploit vulnerabilities in your application.
From scanning code to understanding architecture
The code context graph and security intelligence give AURI a deep understanding of how your application works, not just what is in it. Here's what that looks like in practice.
Deep code reasoning
AURI excels at detecting the vulnerabilities that traditional scanners miss — flaws in business logic, broken access control, and authentication bypasses. During testing, AURI identified multiple zero-days in production applications, including prompt injection in an MCP server.
It does this by building a deep semantic model of your code. AURI's code search understands meaning, not just syntax — it can tell the difference between renaming a function and changing how it works. Its code navigation then builds multi-file, multi-function data flow analysis across your entire codebase, tracing the difference between a library that sanitizes user input and one that bypasses it.
Full-stack reachability
Applications are more than their source code or an inventory of components. AURI maps how all those pieces work together, building a complete graph of how data flows through source code, through direct and transitive dependencies, and into container base images. The result: engineers stop getting paged for vulnerabilities that aren't actually reachable in their application. We've observed up to a 95% noise reduction across each layer: code, open source dependencies, and container images. One financial services customer saw 10X fewer security tickets each month, giving their engineering team back the hours they were spending researching findings that turned out to be false positives.
Agentic remediation
AURI works directly with agents to fix vulnerabilities. Because AURI understands how source code interacts with dependencies, it can recommend safe upgrades or help refactor code to solve breaking changes. It also catches and fixes issues as agents or developers make changes, helping resolve security risks before code is committed, resulting in 83% fewer blocked PRs from security alerts.
Token efficiency
We built AURI to work on enterprise codebases and designed it in close partnership with companies in our design partner program. Cost, efficiency, and scale are non-negotiable in these types of complex environments.
LLM-only approaches use brute-force methods to understand code: they feed large chunks of code directly into an LLM and let it search for problems. That burns through tokens, racks up GPU costs, and doesn't scale efficiently.
AURI takes a different approach. The code context graph and custom tools — code search and code navigation — give agents a way to navigate your codebase intelligently rather than use grep to force their way through. AURI doesn't rescan your code because a variable name changed. It knows when you’ve changed the code's behavior.
The result is a dramatically lower cost per scan and faster results, which matters when you're running security across every commit in an enterprise codebase.
Getting started
Our Skills, MCP, and CLI are free for everyone. Install AURI in minutes inside Cursor, Claude Code, OpenAI Codex, Open Hands, and more — and start writing more secure code today.
For enterprise teams that need AURI's full platform, book a demo.
What's next?
When you're ready to take the next step in securing your software supply chain, here are 3 ways Endor Labs can help: