Most cybersecurity conversations focus on how malware gets in. The phishing email. The dodgy attachment. The compromised website. And yes, that initial foothold matters enormously. But here's the thing that doesn't get nearly enough attention: what happens after the malware lands?
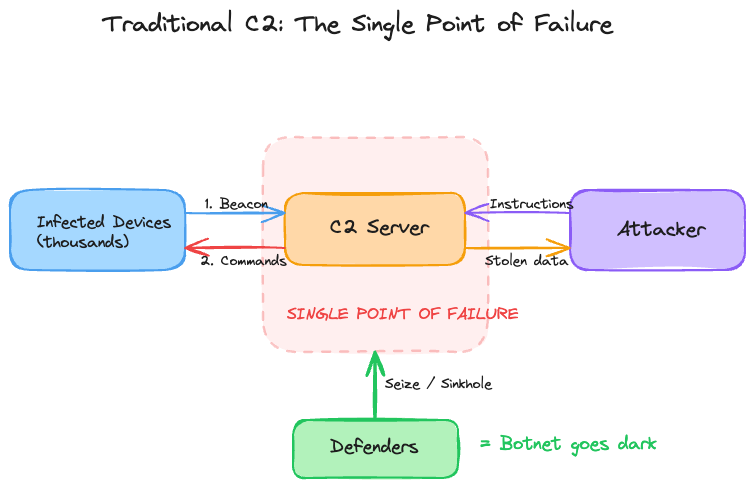
Malware by itself is just code sitting on a computer. To do anything, it needs to communicate, get instructions, report back, and adjust to what defenders do. This back-and-forth between the malware and the attacker's systems is managed by a Command and Control server, or C2.
For decades, the C2 server has been the weak point in every malware operation. If defenders find and remove it, the entire campaign stops.
But now, attackers have found a way to put their C2 infrastructure somewhere it can't be seized, deleted, or shut down: on the blockchain.
Let's look at how this happened, how it works, and why it's causing concern for security teams.
First, let's review how C2 has traditionally worked.
A C2 server acts like mission control for a malware operation. Here’s how it usually works:
Step 1: Malware gets onto a victim's machine, whether through a phishing email, a compromised website, an infected USB drive, or another delivery method.
Step 2: The malware contacts a server controlled by the attacker, usually at set intervals. This is called beaconing—the infected machine regularly checks in with the C2 server to ask if there are any new instructions.
Step 3: The C2 server sends commands, which could include stealing browser passwords, moving to other servers, deploying ransomware, or taking specific files. The malware follows these instructions and reports back.
Step 4: This process repeats. The attacker keeps control of the compromised machine as long as the C2 channel stays open.
To hide this communication, attackers have become more creative over time. Early botnets used IRC channels, which are like group chats, to send commands to many infected machines at once. Today, C2 traffic often looks like normal web browsing, uses DNS queries, or hides within legitimate cloud services. The aim is always to blend in with regular traffic so it goes unnoticed.
But there is a key weakness in this setup, which is why traditional C2 has always been a back-and-forth struggle. The C2 server is a single point of failure. It is a computer with an IP address or domain name, so it can be found. Once defenders or law enforcement identify it, they can seize the server, redirect the domain to a controlled server, or ask the hosting provider to shut it down.
When the C2 server is taken down, the attacker loses control of all infected machines. The botnet stops working.
Attackers have always been aware of this weakness. They have tried to work around it using methods like fast-flux DNS, which quickly rotates through many IP addresses, domain generation algorithms that create new domain names for the malware to find the C2, and using hosting providers in places that ignore takedown requests. These methods make takedowns harder, but there is still a server and a domain name that can be found and seized.
But what if there was no server or domain name to find?
A brief blockchain primer (just enough to understand what comes next)
If you already know about blockchain, stay with me for a moment. It's important to make sure everyone understands, because the same features that make blockchain useful for good purposes also make it powerful for malware infrastructure.
A blockchain is, at its core, a database. But it's a database with three unusual properties:
It's distributed. The data isn't stored on a single server or even in a single data center. It's replicated across thousands of independent computers (called nodes) worldwide. There's no central authority that controls it, and there's no single machine you can switch off to make the data disappear.
It's immutable. Once data is written to the blockchain, it cannot be edited or deleted. Not by the person who wrote it, not by a government, not by the company that created the blockchain. The data is there, forever, baked into the mathematical chain of blocks that gives the technology its name.
It's publicly readable. Anyone can query a public blockchain and read the data it stores. You don't need credentials or permissions. You just need to know where to look.
There is one more concept to cover: smart contracts. A smart contract is a small program that runs on the blockchain. Once deployed, anyone can interact with it by calling its functions, reading its data, or sending transactions that trigger certain actions. It's like a vending machine: you make a request, maybe pay a small fee, and it automatically gives you a result without any human involved.
The key insight is this: if you store data in a smart contract, that data inherits all the properties of the blockchain itself. It's replicated everywhere, it can't be deleted, and anyone can read it.
Including malware.
EtherHiding: the technique that changed the game
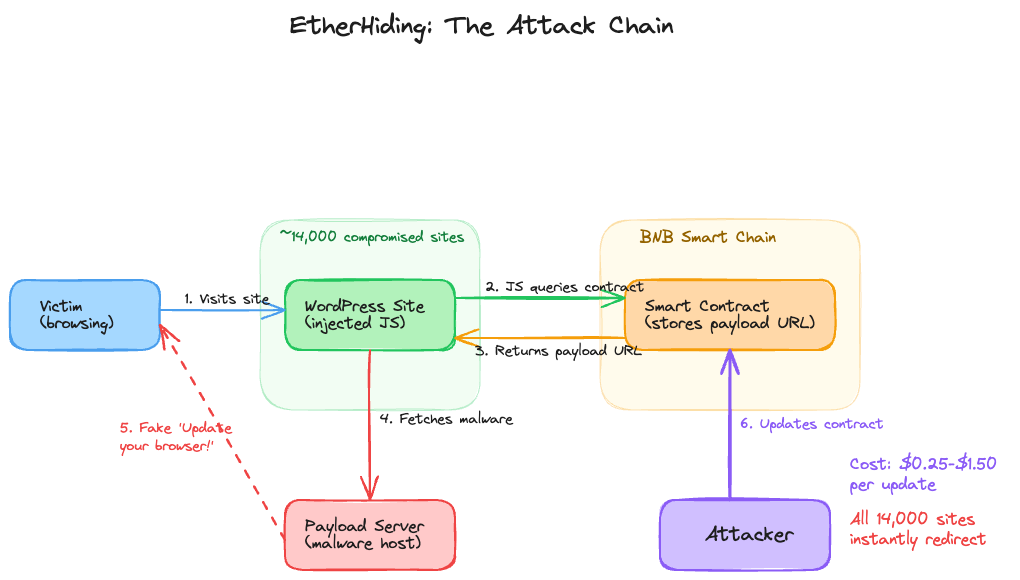
In October 2023, researchers at Guardio Labs published a bombshell finding. They had discovered a technique they called EtherHiding, and it represented a fundamental shift in how attackers could manage their C2 infrastructure.
Here's how it works, step by step. Stay with me, the elegance of this (from a purely technical standpoint) is genuinely remarkable.
Step 1: Compromise a legitimate website. Attackers target WordPress sites, and not just a few. Research from Google's Mandiant team found that about 14,000 WordPress websites have been compromised and used in this infrastructure since late 2023. Attackers use known vulnerabilities or weak passwords to inject malicious JavaScript into the site's pages.
Step 2: The injected script calls a smart contract. Here's where it gets interesting. Instead of the malicious JavaScript containing a hardcoded URL pointing to a traditional C2 server, it makes a call to a smart contract on the BNB Smart Chain (Binance's blockchain). It asks the smart contract a simple question: "Where should I send the victim right now?"
Step 3: The smart contract returns the current payload address. It responds with a URL where the malicious payload is hosted. This changes everything because the payload URL is not stored in the compromised website, but on the blockchain, and the attacker can update it at any time.
Step 4: The visitor sees a fake browser update prompt. The JavaScript uses the URL from the smart contract to display a convincing overlay on the compromised website, usually a fake message saying, "Your browser needs to be updated." If the visitor clicks it, they download malware, often an information stealer like RedLine, Amadey, or Lumma.
Step 5: If defenders block the payload URL, the attacker simply updates the smart contract. In the old model, blocking a malicious URL meant the attacker had to set up a new server, register a new domain, and update all compromised websites, which was slow and costly. With EtherHiding, the attacker sends one transaction to the smart contract, costing between $0.25 and $1.50, and all 14,000 compromised websites immediately point to the new payload location. There is no need to re-infect or change any of the sites. One blockchain transaction redirects the entire campaign.
By late 2024, UNC5142 had evolved further, implementing what's called a proxy pattern, a three-smart-contract system (Router, Logic, and Storage contracts) borrowed from legitimate decentralized application architecture. This gives them on-chain, modular, upgradeable infrastructure. They can swap out the logic of their operation without deploying new contracts, just as a software company can update a web application without changing the URL.
Attackers are now using software engineering best practices. The proxy pattern, a common design in legitimate Ethereum development, is being used to build resilient and maintainable malware infrastructure.
This is not just a single technique. It is becoming a common approach.
If EtherHiding were the only example, it would be worrying but manageable. The real issue is that it is not isolated. Many threat actors, using different blockchains and skill levels, have adopted the same main idea: use the blockchain as the C2 backbone.
North Korean state actors joined the party. Starting in February 2025, a group tracked as UNC5342, linked to North Korea's cyber operations by Google/Mandiant, incorporated EtherHiding into their social engineering campaigns targeting cryptocurrency developers. But they added a twist. Instead of storing C2 information in smart contract storage, they embed it in the calldata of blockchain transactions, the raw input data attached to a transaction that is permanently recorded on-chain. The malware doesn't read from a contract; it reads the attacker's transaction history and extracts the latest instructions from the most recent transaction. This is what the security community calls a dead-drop resolver, a Cold War-era espionage concept adapted for the blockchain age. The result? DPRK-linked cryptocurrency heists powered by instructions that literally cannot be censored or removed.
The Aeternum C2 botnet made it a product. In what is perhaps the most alarming development, a threat actor using the handle "LenAI" began advertising the Aeternum C2 botnet on underground forums in December 2025. Aeternum is a native C++ loader that stores encrypted commands on the Polygon blockchain. It comes with a slick web panel where customers can select a smart contract, choose a command type, specify a payload URL, and push updates, all written to the blockchain as transactions that every infected device polls for. The pricing? $200 for panel access and a configured build. The operational costs are almost comical: $1 worth of MATIC (Polygon's native token) covers 100 to 150 command transactions. For $4,000, you can buy the entire source code. This is the commoditization of blockchain-based C2, you no longer need to understand smart contracts, Solidity, or blockchain architecture. It's point-and-click.
GlassWorm brought it to Solana. A supply-chain attack dubbed GlassWorm took a different approach entirely, querying a Solana wallet's transaction memo field every 5 seconds to retrieve C2 instructions. Different blockchain, different mechanism, same fundamental principle: the command infrastructure lives on a distributed ledger that nobody controls.
npm supply-chain attacks added another vector. In late 2024, researchers discovered malicious npm packages using Ethereum smart contracts to retrieve their C2 server addresses. The packages themselves contained no hardcoded malicious URLs, they'd call a smart contract at install time, get back the current C2 address, and phone home. If the C2 server got taken down, the attacker could update the smart contract to point somewhere new, and every new installation of the package would automatically connect to the updated address.
The trend is clear: this technique is spreading across different blockchains (Ethereum, BNB Smart Chain, Polygon, Solana), attack types (web compromises, supply-chain attacks, social engineering), and threat actor groups (criminals, nation-state operators, and now malware vendors). It is no longer a niche method. It is becoming a standard tool for attackers.
Why this is such a headache for defenders
To see why blockchain-based C2 is such a challenge, it helps to look at the specific advantages it gives attackers, especially compared to the traditional model.
There is no server to seize. In the traditional model, the C2 server is a physical or virtual machine with a hosting provider, an IP address, and a location. Law enforcement can get a warrant, take the hardware, and redirect the domain. With blockchain-based C2, the 'server' is the blockchain itself, a distributed network of thousands of nodes worldwide. There is no hosting provider or domain registrar to contact, and no single machine to seize. As long as the blockchain runs (and major chains like Ethereum and BNB Smart Chain have nearly 100% uptime), the malicious infrastructure stays online.
Immutability means the data lasts forever. Once malicious data like a payload URL, C2 address, or encrypted command is written to the blockchain, it cannot be removed, not by developers, courts, or law enforcement. Even if the attacker is caught, the infrastructure remains. The Aeternum C2 creators highlight this: even if all infected machines are cleaned, the operator can redeploy using the same contracts without rebuilding.
Updates are cheap and instant. In the traditional model, moving a C2 server means setting up new servers, registering new domains, and updating botnet configurations, which takes time and money. With blockchain-based C2, an update costs only pennies and happens instantly. In UNC5142's campaign, a single transaction costing a dollar or less redirected 14,000 compromised websites to a new payload source. The speed difference is significant, by the time defenders block a malicious URL, the attacker may have already switched to several new ones.
It looks like legitimate traffic. Here's a subtlety that makes network-level detection very difficult. Infected machines do not connect directly to blockchain nodes, since running a full node uses too many resources.Instead, they use public RPC gateways from companies like Infura, Alchemy, and Ankr, the same ones used by millions of legitimate Web3 apps, DeFi platforms, and crypto wallets. So when defenders see HTTPS connections to mainnet.infura.io, it could be a developer, a user, or malware getting instructions.Telling them apart at the network level is very hard.
This technique is becoming commoditized, which is a major concern. When a method requires deep expertise, only skilled attackers use it. But when it is packaged in a web panel and sold for $200, as Aeternum has done, anyone with cryptocurrency can use it. The barrier to entry is now very low.
So what can defenders actually do?
It's important to avoid two extremes: thinking the situation is hopeless or believing that buying a product will solve everything. The reality is more complex.
Blockchain-based C2 does remove one of the defender's strongest tools, infrastructure takedown. However, it does not make the whole attack chain invisible. There are still practical steps defenders can take.
Monitor for anomalous blockchain interactions. Most enterprise endpoints have absolutely no legitimate reason to be querying blockchain RPC endpoints. If your accounting department's workstations are making HTTPS calls to Infura or Alchemy, that's a red flag worth investigating. Elastic Security has published detection rules specifically designed to flag potential EtherHiding C2 connections based on network behavior patterns.
Focus on the chokepoints. Decentralized malware still relies on centralized gateways. Running a full blockchain node is not practical for infected machines, so the malware uses public RPC providers like Infura, Alchemy, and Ankr. These providers become chokepoints. Defenders can block certain RPC endpoints at the network level or work with providers to block known malicious contract addresses. While you can't take down the blockchain, you can block the paths malware uses to access it.
Focus on the rest of the kill chain. Blockchain-based C2 is just one link in the attack chain. The initial compromise (WordPress vulnerabilities, social engineering, supply-chain attacks), the payload delivery, and the endpoint execution are all still thoroughly conventional. Endpoint Detection and Response (EDR) platforms can identify malicious loaders attempting to retrieve commands from external sources. Behavioral analysis, memory inspection, and anomaly detection remain effective methods for catching malware regardless of how its C2 channel is architected. Patching WordPress sites, auditing npm dependencies, and training users to recognize social engineering, all the basics, still matter enormously.
Invest in blockchain intelligence. This is a new but important area. Security teams and blockchain analytics companies are building ways to monitor on-chain activity for known malicious contract addresses, track the funds used to run these contracts, and spot patterns in smart contract code that suggest malicious intent. The transparency of public blockchains allows defenders to see what attackers are doing, just as it helps malware. All the data is public. The challenge is having the right tools and skills to analyze it at scale.
The asymmetry problem
The properties that make distributed ledgers valuable for legitimate use, censorship resistance, immutability, global availability, permissionless access, are precisely the properties that make them so effective as malware infrastructure. This isn't a bug that blockchain developers can patch. It's a fundamental characteristic of the technology. Asking a blockchain to be "un-censorable, except for malware" is a bit like asking the internet to be "open, except for bad people." The feature and the vulnerability are the same thing.
In practice, the old approach of finding and taking down the server is becoming less effective against advanced attackers. Defenders need to shift their focus. Instead of trying to destroy the attacker's infrastructure, they should focus on detecting malware behavior on endpoints, blocking its communication channels, and using blockchain transparency to gather intelligence against attackers.
Attackers have found a command channel that is nearly impossible to destroy. Now, defenders must make that channel useless by stopping malware before it can connect, or by ensuring it cannot get any useful information if it does.
This is a more difficult problem than taking down a server, but it is not impossible.
What's next?
When you're ready to take the next step in securing your software supply chain, here are 3 ways Endor Labs can help:










