Malware in the software supply chain is surging. More than 90% of all malware advisories for open source software ever filed landed in 2025 alone. The threat is evolving fast. Organizational defenses are not.
That gap — between what organizations know and what they do, is the central finding of Malware in the Open Source Ecosystem, a new report from the Endor Labs security research team. Based on a survey of 605 IT professionals combined with original analysis of the Open Source Vulnerability (OSV) database and npm package metadata, it quantifies how fast the threat is growing, where defenses are falling short, and why the organizational response hasn't kept pace.
The threat is accelerating
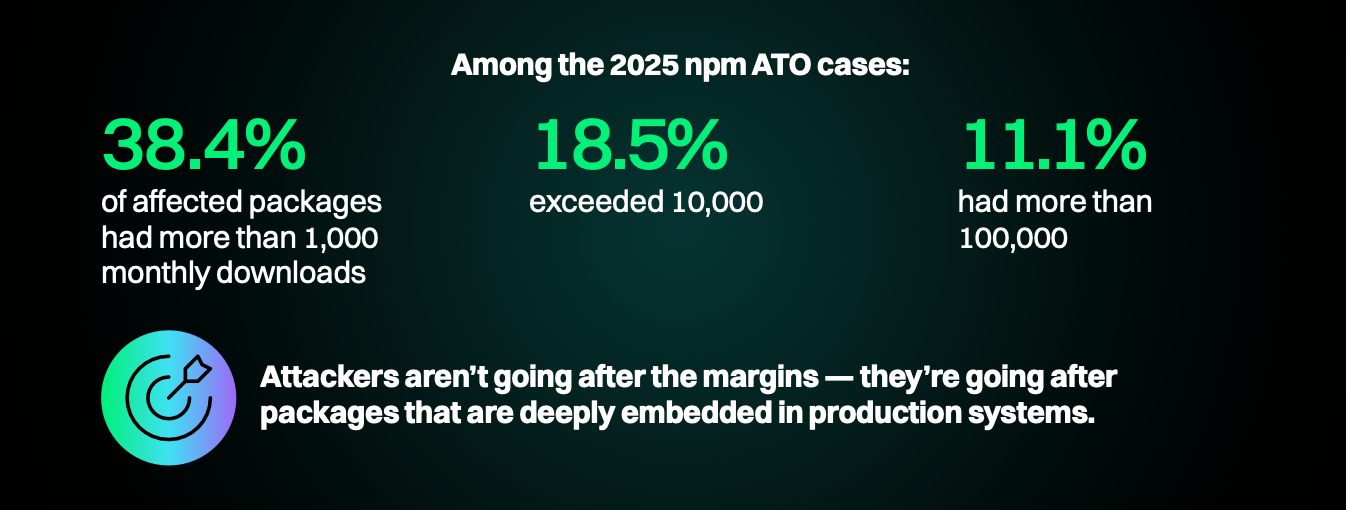
Account takeovers (ATOs) — where an attacker compromises a maintainer’s credentials and publishes a malicious version under a trusted package name — emerged as one of the most dangerous vectors in 2025. Of the 1,011 npm ATO advisories recorded in the OSV database over all time, 930 were filed in 2025, a roughly 12x year-over-year increase representing 92% of all ATOs reported on npm.
These are not obscure packages. Among the 2025 npm ATO cases, 38.4% of affected packages had more than 1,000 monthly downloads, 18.5% exceeded 10,000, and 11.1% had more than 100,000. Attackers are deliberately targeting packages that are deeply embedded in production systems and automated CI/CD pipelines, maximizing the blast radius of each compromise.
Attacks are escalating
We started this investigation following the well-known Shai-Hulud campaign and other high-profile package compromises in the second half of 2025. Since we closed the survey in early February, the pace of software supply chain attacks has only intensified.
The group known as TeamPCP started with one incomplete incident response at Aqua Security in late February and, in under 30 days, escalated across five ecosystems: GitHub Actions, Docker Hub, npm, OpenVSX, and PyPI. Each compromise yielded credentials that unlocked the next target — from Trivy and KICS to litellm (95 million monthly downloads) to telnyx three days later.
Yesterday's axios compromise followed a similar playbook: hijack a maintainer account, add a postinstall hook to pull in a typosquatted package, and rely on automated pipelines to distribute it before anyone notices. Although the attack has been attributed to a different group linked to North Korea, it represents the ongoing escalation of attacks across the open source ecosystem.
Responsibility is everywhere, accountability is nowhere
Despite widespread awareness and concern, our research documents a consistent and concerning pattern: organizations understand the threat of software supply chain attacks but haven't operationalized that understanding into robust security programs.
- Priority without investment: 81% of organizations say malicious open source software is a top security priority, yet fewer than half (48%) expect their spending on OSS malware prevention and detection to increase in 2026.
- Awareness without action: 88% of respondents know that the first days after a package release are the highest-risk window, yet only 21% enforce cooldown periods — one of the sharpest disconnects in the survey.
- Half already affected: 51% of organizations identified suspected or confirmed malicious packages in their environments in 2025. For more than half the industry, this is a current operational reality, not a future risk.
The report identifies fragmented ownership as a root cause of slow response. Responsibility for malicious OSS spans at least four functions — engineering, application security, cloud security, and security operations — but no single team owns the full program.
As a result, response times compound the problem. Respondents in security operations and incident response roles were 2x more likely to report having no visibility into their organization’s dependency intake controls, even though they are the ones called when an incident occurs.
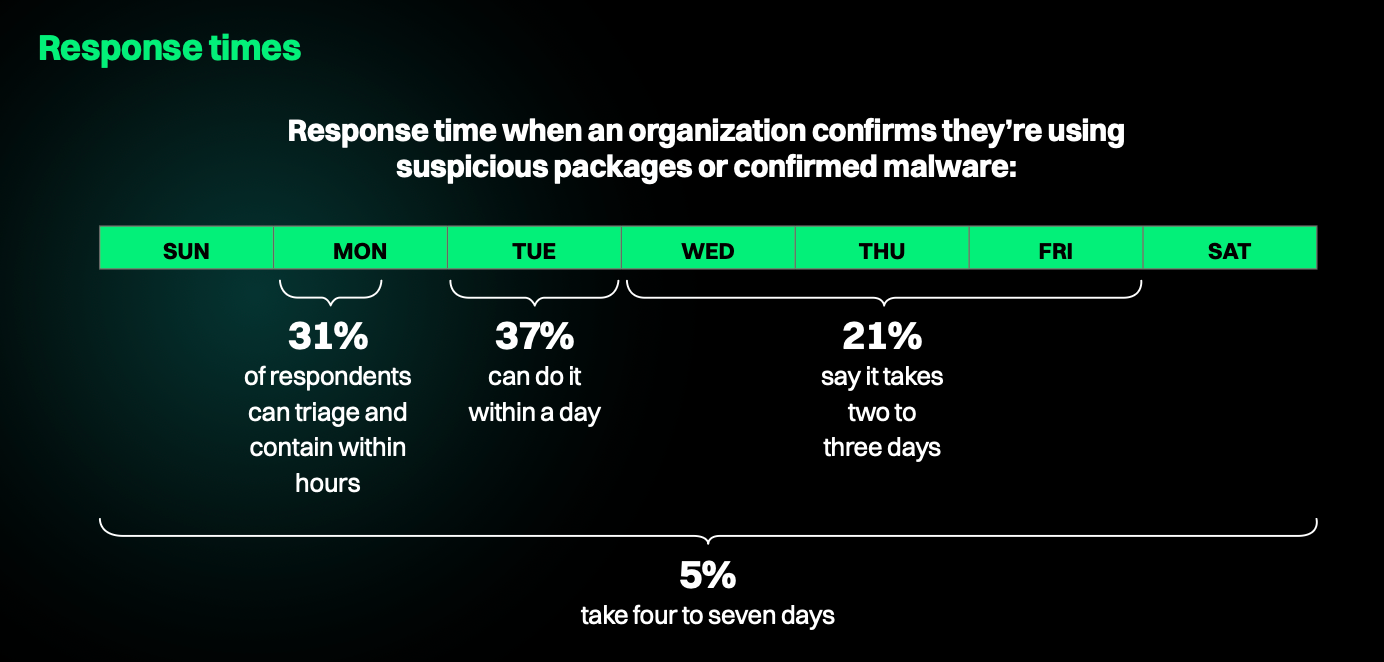
While 31% of organizations say they can triage and contain a confirmed malicious package within hours, 26% take two days or more, a window in which a compromised dependency can exfiltrate credentials, harvest secrets, and establish persistence across cloud environments.
Hear from the researchers
Join us for a live webinar at the end of April. We’ll walk through the findings from Malware in the Open Source Ecosystem, field your questions on the current threat landscape, and discuss practical steps for building a cross-functional malware response program at your organization.
What's next?
When you're ready to take the next step in securing your software supply chain, here are 3 ways Endor Labs can help: