FedRAMP compliant, developer approved.




















How Endor Labs reduces your FedRAMP burden

.webp)
FAQs
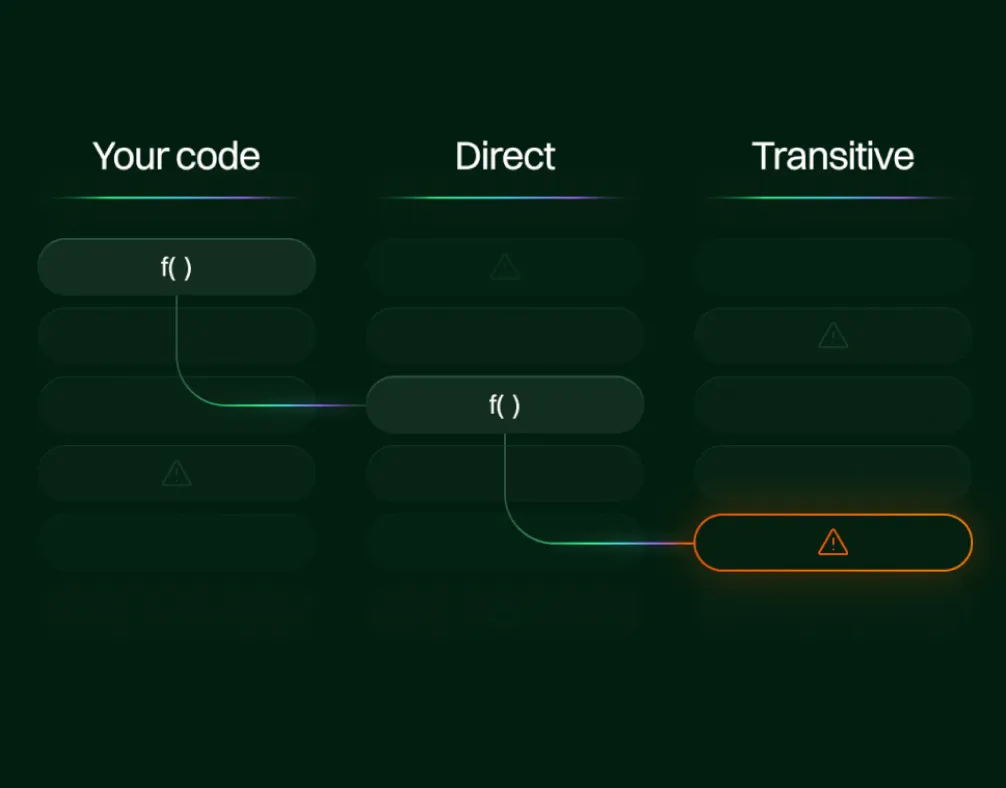
Not quite. FedRAMP requires you to fix every exploitable vulnerability, but it also has a deviation request process that allows you to document findings as false positives if you can demonstrate they aren't reachable in your application. Endor Labs' function-level reachability analysis has been evaluated by leading FedRAMP PMO and several 3PAOs (including Fortreum and Schellman), and it meets their standard for false positive identification. That means you can use it to justify deviation requests rather than remediating vulnerabilities your application never actually calls.
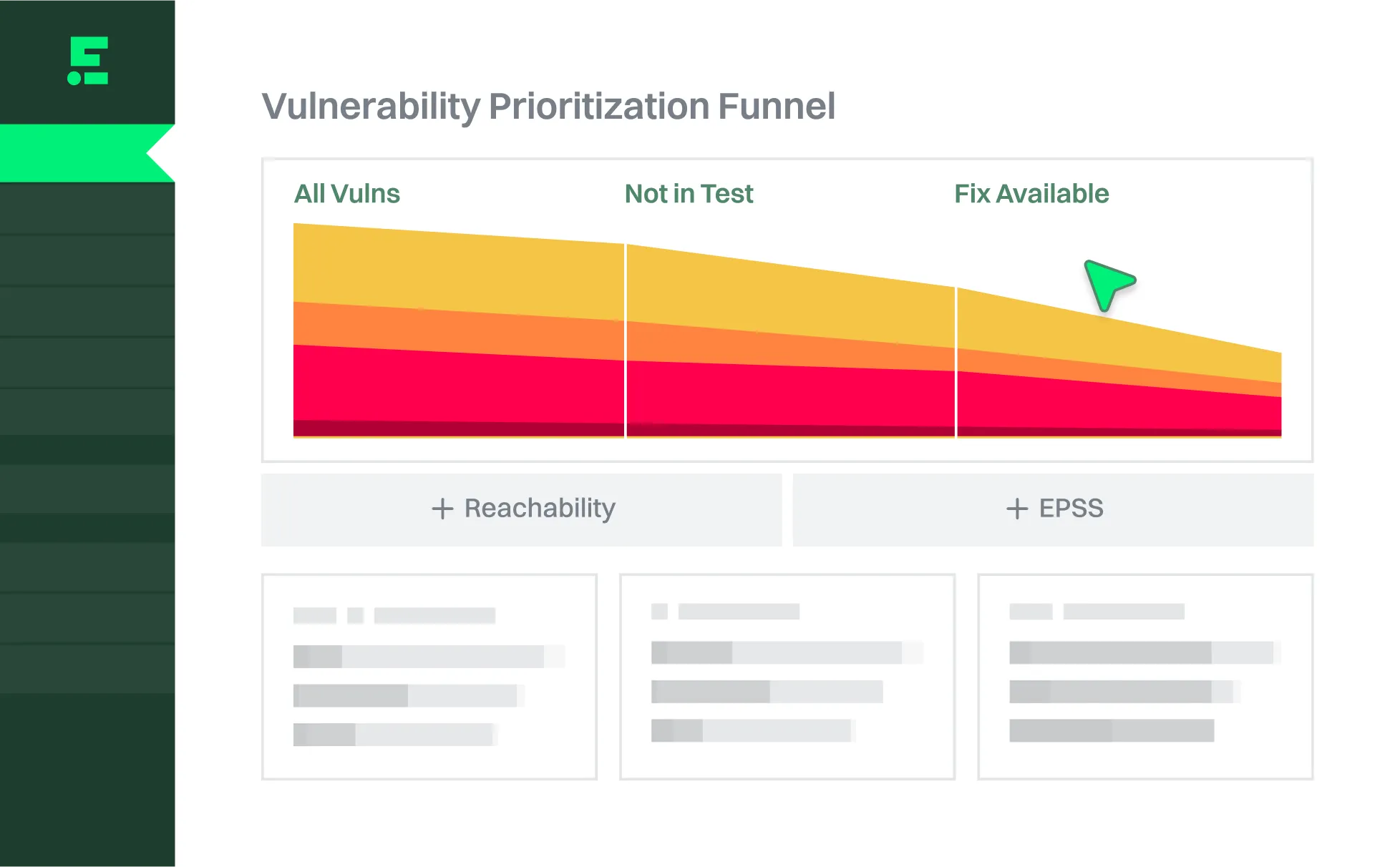
Most SCA tools identify vulnerabilities based on manifest files, which are often incomplete and lack the context to distinguish exploitable findings from noise. For FedRAMP, that matters because every finding your tool surfaces has to be documented, tracked, and either remediated or justified as a false positive. Endor Labs goes further by analyzing your actual application code to understand which vulnerable functions are reachable at runtime, and by correlating SCA findings with container scan results to eliminate duplicate POA&M entries.
FedRAMP doesn't allow you to group vulnerabilities, but it does allow deduplication when two tools find the same issue. Without native correlation, SCA and container scanners produce separate findings for the same vulnerability, each requiring its own POA&M entry. Endor Labs automatically correlates results across scan types so one vulnerability produces one entry, and extends reachability analysis through container image OS layers to filter out findings that aren't reachable at runtime.
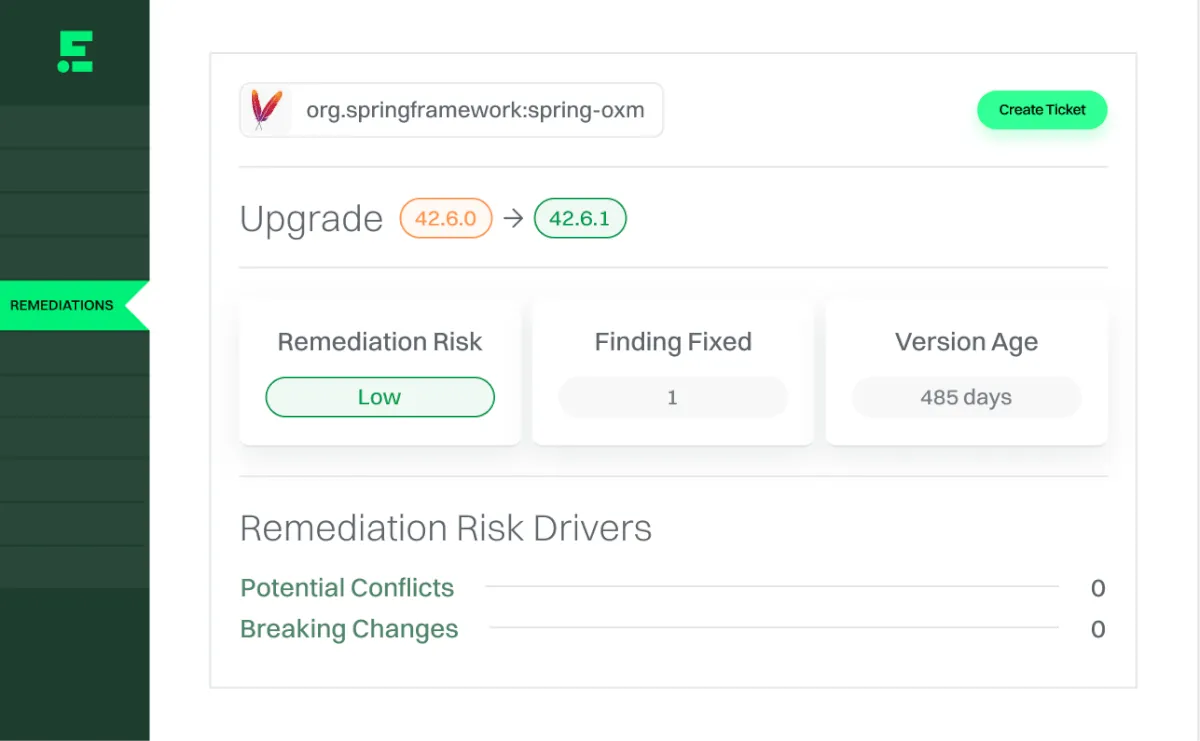
The biggest driver of missed SLAs is spending time on vulnerabilities that don't need to be fixed. By reducing your remediation workload by 70-80% on average, Endor Labs gives your team more time to focus on findings that are real and urgent. For the fixes that remain, Upgrade Impact Analysis shows you the complexity of each remediation before your team commits to it, and Endor Patches let you remove risk at build time when an upgrade can't be completed within the SLA window.
Endor Labs automatically generates Software Bills of Materials (SBOMs) and Vulnerability Exploitability Exchange (VEX) documents with every scan. These give your 3PAO the evidence trail they need to approve deviation requests for false positives, and make it straightforward to demonstrate continuous monitoring coverage without manual documentation work between assessment cycles. The platform is also API-native, so you can pull Endor Labs’ data into your other workflows to ensure reporting is automated and low-effort.