Endor Labs Supply Chain
Take a new approach to governing open source code and CI/CD pipelines with a platform that saves time and accelerates product development.


Support a modern SDLC
Adopt security tools that address modern coding trends and offer API-first integration into the SDLC.
Manage emerging risks
Build a security program that addresses risks brought in by 3rd parties and human error.
Make developers faster
Make "shift left" a reality with non-intrusive security processes that prioritize developer experience.

Trusted by leading teams






























































There's a better way to SCA
Endor Labs Open Source
SCA and so much more
Reachability analysis
Remediation assistance
Container image scanning
OSS Top 10, including malware
SBOM / VEX and artifact signing
Endor Labs CI/CD
Ship code you can trust
CI/CD pipeline visibility
Repository security posture management
Build integrity verification
GitHub Actions security
Endor Labs Compliance
Comply with requirements
Single hub for 1st and 3rd party SBOMs
Automated VEX generation
Accelerate compliance for NIST SSDF, FedRAMP, and PCI-DSS 4.0
Endor Labs Secret Detection
Stop costly leaks
Scan SDLC from pre-commit to git history
Prioritize valid secrets
Custom policies to support unique workflows

Software development is now software assembly.
Trends in software development
To meet the demands of customers, organizations have widely adopted agile and other iterative development methodologies that shorten release cycles and accelerate feature delivery. Four trends are influencing the progression of modern software development - and the tactics needed to secure it:
- Trend 1: Open Source Software (OSS)
70-90% of code in actively-developed projects is imported via OSS dependencies.
- Trend 2: Artificial Intelligence (AI)
Beginning in 2023 with the explosive growth of generative AI and large language models (LLMs), AI models are another tool to accelerate development and beat competition.
- Trend 3: Continuous Integration and Delivery
CI/CD pipelines enable automation of various development activities along the software development lifecycle (e.g. compilation, unit and integration tests or packaging)
- Trend 4: Containerization
Modern applications are run in containers, which allows for applications to be lightweight, portable and standalone, enabling scalability, replication, and re-use.
Enterprises struggle to manage emerging risks.
Protecting software gets harder every day
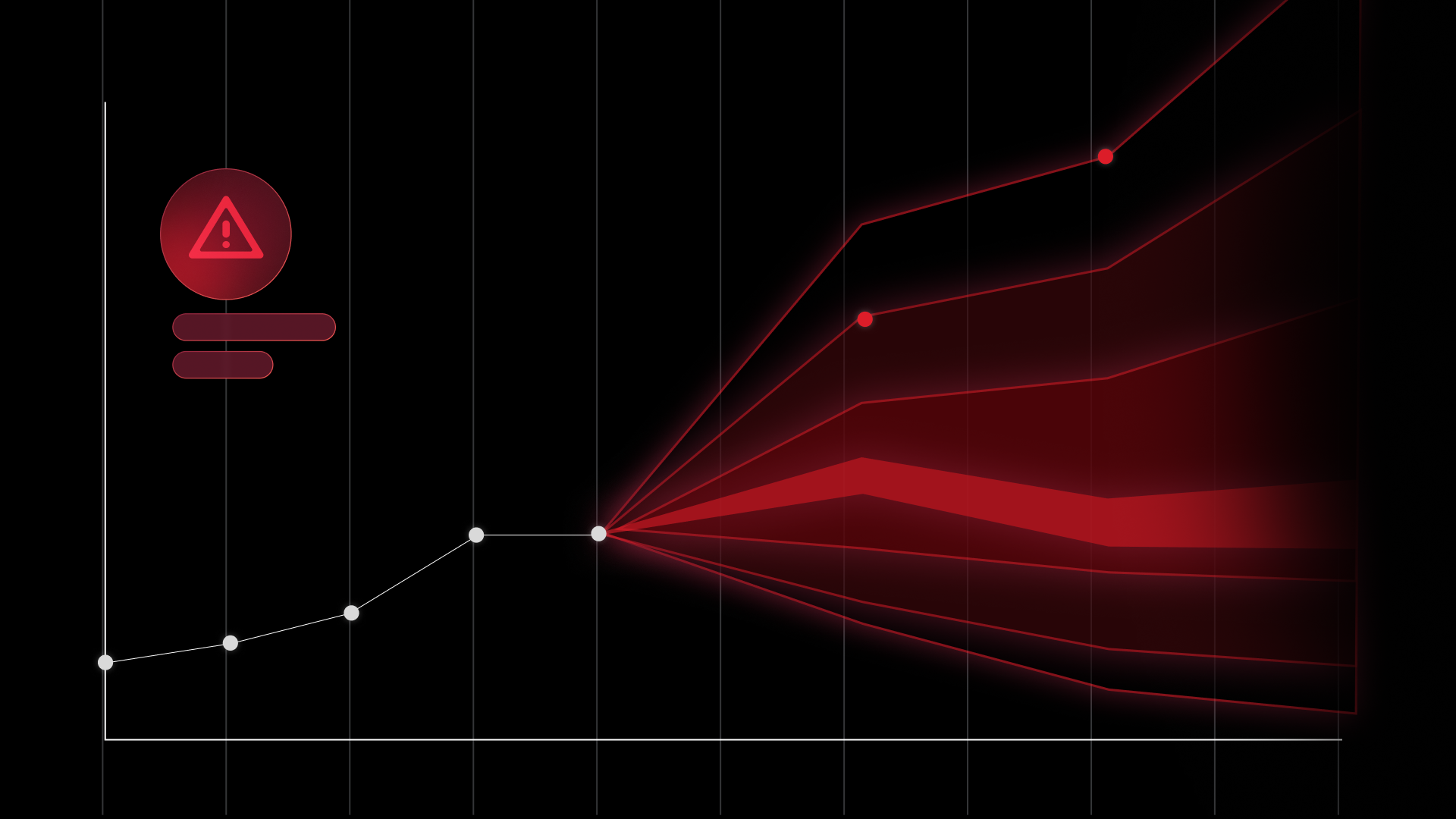
Software supply chain security continues to be one of the most widely discussed topics in the cybersecurity industry, and rightfully so. In 2023, Capterra found 61% of U.S. businesses were directly impacted by a software supply chain attack within the past 12 months. Reports estimate a 742% increase in software supply chain attacks in the last several years and a three-fold increase in malicious packages from 2022 to 2023. These include attacks against both proprietary software vendors and their products, as well as widely used open source software (OSS) projects and components.
Organizations face three specific challenges:
- Challenge 1: They are using more OSS than they think
...and AI is accelerating it while security tools struggle to secure it. For recommendations around OSS governance, read How to Evaluate Your Open Source Security Posture.
- Challenge 2: Shadow CI/CD pipelines are on the rise
...and what you don't know can definitely still hurt you. For an overview of emerging CI/CD challenges, read Introducing CI/CD Security with Endor Labs.
- Challenge 3: Compliance burdens continue to increase
...and we can expect more new rules, regulations, and frameworks in 2024. Explore our Compliance & SBOM resources to catch up on new regulations and practices.
Security tools should make you more productive.
Were your tools built for speed?
If your security programs are failing to deliver results, it may be tempting to blame your developers (they aren't remediating vulnerabilities!), but developers aren't at fault. It's your security tools. Taking SCA as an example, our research shows that traditional SCA tools produce an average false positive rate of 80%. That means 4 our of 5 issues are false alarms.
This matters because developers get frustrated by security noise. They get so many false alarms that they become dismissive of tools and risks. The AppSec team has to chase them to get things fixed, and application security becomes seen as an annoyance. Application security is seen as unachievable and because you can't prove the value of your programs, investment in AppSec decreases. Which means you can't invest in new tools that quiet the noise and reduce your risks. And the cycle continues.
Rachit Lohani, CTO of Paylocity, said it best:
"Shift left was all about enabling teams to do more. But it became a responsibility shift instead of shifting where it happens in the process."
Embrace modern software development with Endor Labs
We believe developing secure software shouldn't be rocket science.
Endor Labs is a software supply chain security (SSCS) platform for organizations that value developer experience. We help DevSecOps teams build credibility with developer-centric tools that make it safer and faster to use OSS code, easier to detect CI/CD risks, and simpler to comply with SSCS regulations. Existing Software Composition Analysis (SCA) and Application Security Posture Management (ASPM) tools bury teams in uncontextualized data and tens of thousands of false positive alerts. Endor Labs’s new approach cuts 80% of the noise while providing actionable fix information that actually makes developers faster.
The Endor Labs Supply Chain addresses three key pain points and outcomes:
- Open Source Code Security: Endor Labs helps engineers improve application performance and minimize attack surface by selecting and maintaining secure & high quality dependencies across the SDLC. Endor Labs replaces the existing breed of SCA solutions that lack context on code usage, thereby cutting ~80% of SCA noise so teams can focus on what matters.
- CI/CD Pipeline Security: Endor Labs helps you discover pipelines and shadow engineering, ensure consistent security tool coverage, monitor the posture of repositories, and implement build integrity verification, all through a single hook and policy-as-code framework integrated into your pipeline.
- Compliance & SBOM: Endor Labs helps teams adhere to standards and regulations by detecting legal risk, generating and ingesting SBOMs/VEX, code signing, and align with NIST SSDF and CIS frameworks.
Endor Labs greatly reduced our CVE backlog, which helps satisfy the near zero tolerance for vulnerabilities often seen in highly regulated markets."
Endor Labs greatly reduced our CVE backlog, which helps satisfy the near zero tolerance for vulnerabilities often seen in highly regulated markets."
Integrations and Languages
Our Language Support